While testing an file upload functionality with Burp’s Repeater I noticed the site response changed depending on the file being uploaded, which is normal if the server is validating the file headers.
After a few requests with different responses I got tired of doing this manually and decided to use Burp’s Intruder feature. I quickly noticed that there is no way of telling the Intruder to inject the contents of a list of files in the request.
So I wrote an extension that reads a folder files and feeds their content, one at a time, as a payload to use in the Intruder.
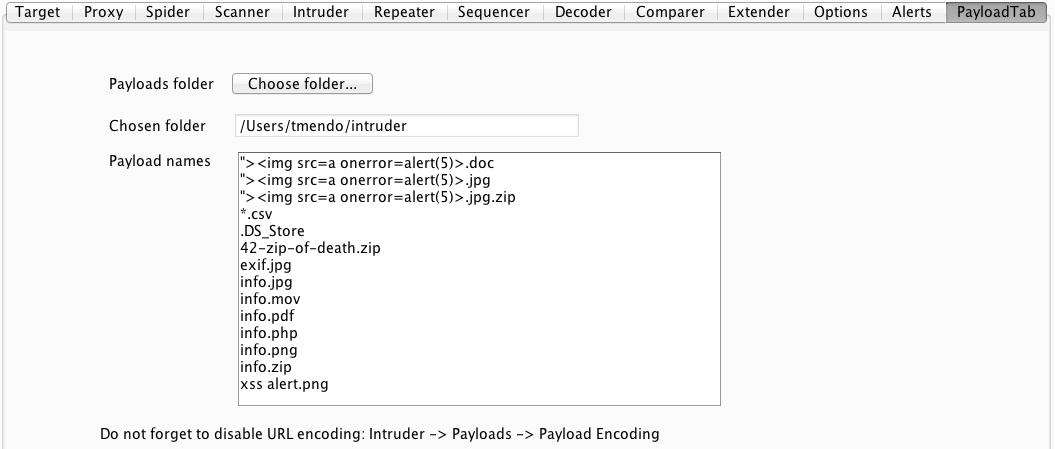
Suppose you have a folder with your best malicious files, zip and xml bombs, jpegs with other contents, php shells, etc. You point the extension to this folder and just use the Repeater normally, setting the payload source as being this extension.
If you need/want to synchronize the file contents with the file name, the extension tab shows the names of the files it just read so you can use them as payload for a second position in the request, using the pitchfork attack.
EDIT
There is a new version of the extension that provides two generators, one for the file name and other for the file contents, easing this synchronization process. See this update post.
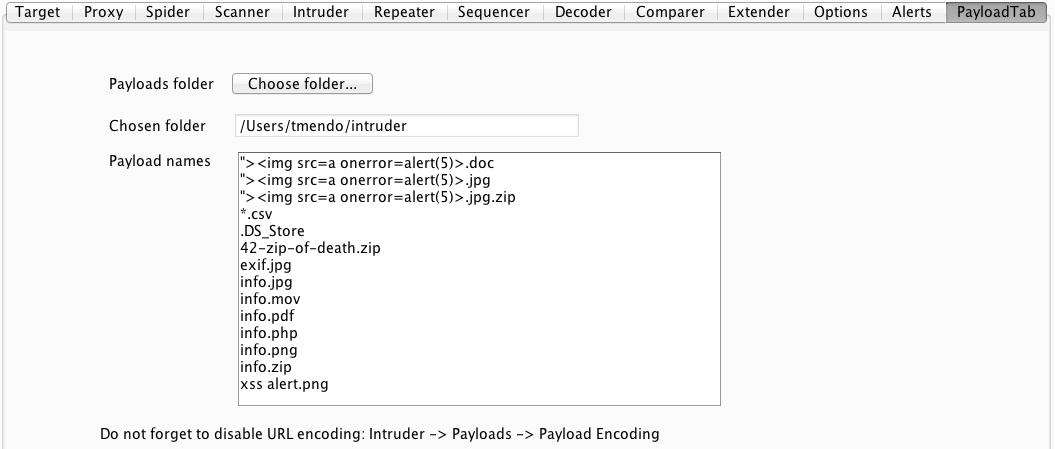
Choosing the input files
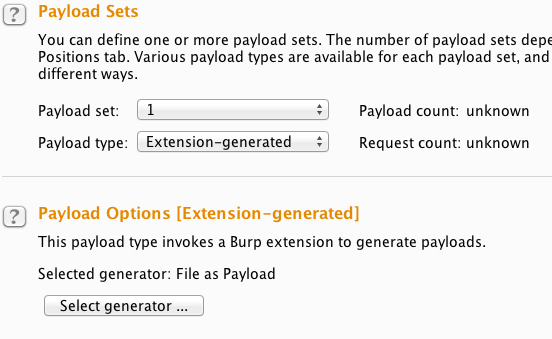
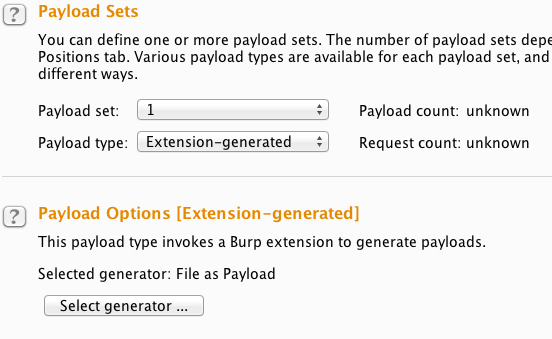
Configuring the Intruder
The extension is available here as a single jar. The code is available here.
I have submitted it to the BApp Store but it hasn’t been approved yet.
EDIT
Now available at the BApp Store, here :)
Enjoy.